4
EDITION OF
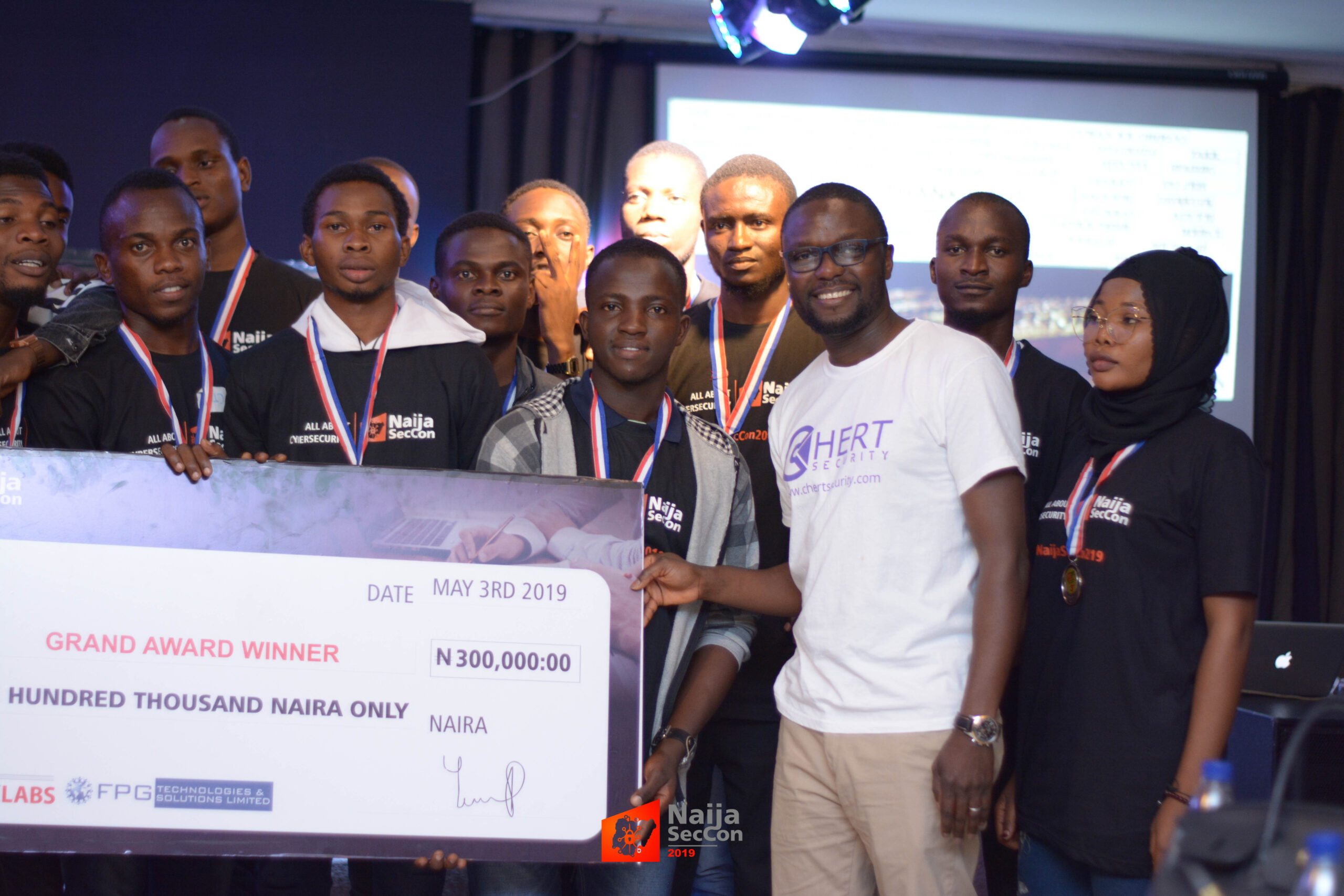
NAIJA SEC CONFERENCE
NAIJA SEC CONFERENCE
NaijaSecCon2020 is planned to attract over 500 cybersecurity professionals from various industries including Financial Services, Insurance firms, Telecommunications, Oil and Gas, conglomerates, Tech Start-ups, Financial Technology (FinTech) companies, other privately-held organizations and also government Ministries, Department and Agencies (MDAs).
LEARN MORE[ SPEAKERS ]
Call-For-Papers is currently ongoing. Selected speakers will be announced soon.

Gbenga Sesan
Executive Director, Paradigm Initiative

Confidence Staveley
Country Manager, DIGISS LLC & Founder #NoGoFallMaga

Dr. Aderonke Thompson
Lecturer, Department of Cyber Security, FUTA

Tosin Amoo
PCN Co-Ordinator - Chevron Nigeria Limited

Abumere Igboa
CISO, Stanbic IBTC Holdings

Ogundipe Boluwatife
Cyber Security student, FUTA

Adediran Moses
400 Level Cyber Security student, FUTA
2
Days
4
Edition
7
Speakers
10
Sponsors
1
Venue
3
Tickets